Working in the Cyber Threat Intelligence (CTI) space, you develop a certain immunity to surprise, or so you think. Even the most hardened organizations, those with seemingly impenetrable security postures and multi-million dollar investments in SOC, can be compromised. However, when Harvard University, a 389-year-old institution with an annual operating budget in excess of $ 6 billion, shows up on Cl0p's data leak site with 1.3 terabytes of exfiltrated data, serves as a stark reminder: in today's threat landscape, no organization is too prestigious, too well funded or too technologically advanced to be immune
The attack vector: zero-day exploit at scale
What makes this incident particularly noteworthy from a threat intelligence perspective is the modus operandiCl0p exploited a critical zero-day vulnerability (CVE-2025-61882, CVSS 9.8) in Oracle's E-Business Suite (EBS) to achieve unauthenticated remote code execution (RCE). This was not a phishing campaign or a supply chain compromise, it was a sophisticated exploitation of enterprise-grade software that affected potentially hundreds of organizations simultaneously.
According to telemetry from Google and Mandiant's Threat Intelligence Group (GTIG), the exploitation has already begun. by July 2025, The attackers maintained persistent access for months before the massive extortion began in early October. The FBI characterized this vulnerability as a stop what you are doing and patch it immediately« situation, terminology reserved for the most critical threats.
What was compromised: beyond surface-level breach notifications
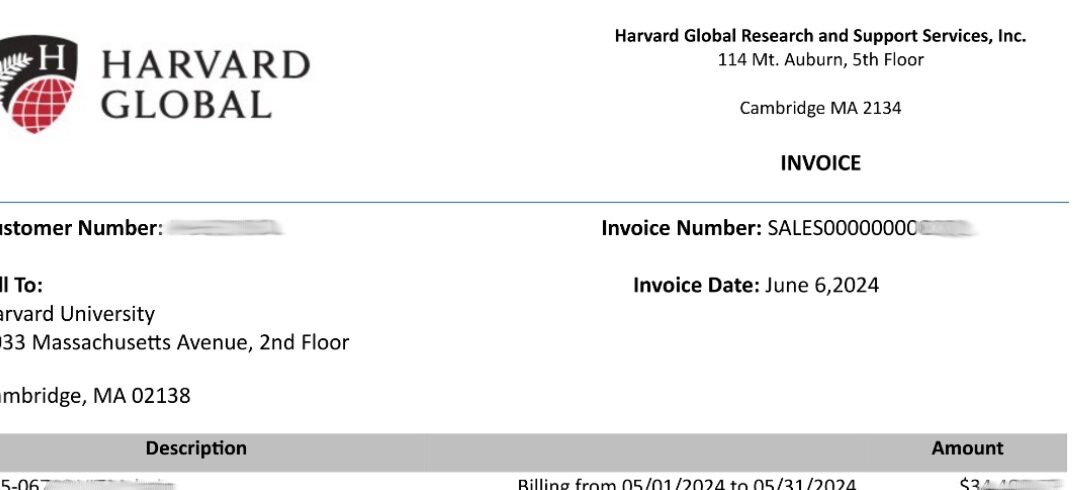
Our analysis of the exfiltrated dataset, leveraging AI-driven data classification algorithms and pattern recognition models trained on PII detection, reveals that the breach primarily affected Harvard Global's Oracle EBS infrastructure. The exfiltrated data includes:
- Journal entries and accounting transactions covering several fiscal periods (2019-2025)
- Multi-currency financial records (TND, GBP, NIS, ZAR, USD, INR) indicating exposure to international transactions
- Payroll data that contain employee compensation information
- Supplier payment records and details of related company transactions
- Internal source code of Harvard's administrative systems
The naming conventions and schema structures observed in the corpus of leaked data confirm an Oracle E-Business Suite architecture, a finding consistent with field analysis conducted through the automated ERP fingerprinting capabilities of our threat intelligence platform.
The Regulatory Dimension: Massachusetts' Breach Notification Obligations
Beyond the technical aspects of this incident, Harvard now faces significant regulatory obligations under Massachusetts Data Breach Notification Law (MGL c. 93H). This statute requires that organizations that possess personal information of Massachusetts residents must report security breaches to:
- Massachusetts Attorney General
- The Director of Consumer Affairs and Trade Regulation
- All affected persons
Notification is required by law «without unreasonable delay», balancing the needs of police investigations with the imperative to restore the integrity of the system. Failure to comply carries serious consequences: organizations may face civil litigation under the Chapter 93A (Massachusetts Consumer Protection Act), which can result in triple damage, The amount of the claim, attorney's fees and court costs.
Given that the leaked dataset includes payroll information, almost certainly containing SSNs, addresses and compensation details of Massachusetts residents, Harvard's notification obligations are unambiguous. The clock is ticking.
The strategic reality: why APTs remain at the forefront of corporate defense
This gap illuminates an uncomfortable truth that CTI professionals viscerally understand: adversaries operate with temporal and tactical advantages that technology alone cannot neutralize. Cl0p maintained access to Harvard's systems during months before Oracle acknowledged the existence of the vulnerability. No EDR solution, no SIEM correlation rule, no AI-driven anomaly detection platform prevented this intrusion.
Consider Cl0p's track record: the 2023 MOVEit transfer campaign (CVE-2023-34362) engaged more than 2,000 organizations and generated an estimated $ 75 million in ransom payments. Prior to that, Accellion FTA (2020-2021), GoAnywhere MFT (CVE-2023-0669) and now Oracle EBS. The pattern is consistent: identify a high-impact zero-day in enterprise infrastructure software, exploit it on a large scale, exfiltrate data and extort.
Advanced persistent threat (APT) groups and ransomware-as-a-service (RaaS) operators such as Cl0p are not only ahead of the game, They are playing a completely different game. While enterprises invest in prevention and detection controls, threat actors focus on:
- Zero-day research and acquisitionDiscover or purchase vulnerabilities before vendors know they exist.
- Persistence and stealthOperating undetected for extended periods of time (average dwell time: 21 days according to Mandiant M-Trends 2025).
- Supply chain objectivescompromised software that companies depend on but cannot easily replace
- Tactical patienceWait for the maximum impact before activating the alarms.
The real answer: resilience over prevention
If Harvard, with its resources, talent pool and institutional sophistication, can be breached through zero-day exploitation, what hope do smaller organizations have? The answer is not in prevent all intrusions (an impossible standard), but rather on building resilience frameworks that embrace the commitment to.
This requires a paradigm shift in the way we design security programs:
- Assuming an infringement mentalityDesign networks, access controls and data architectures assuming adversaries have already penetrated perimeter defenses. Implement zero trust segmentation, least privilege access and continuous verification.
- Operational readiness for partial knowledge scenariosIncident response strategy workbooks should work when the full scope of the risk is not known. Can your IR team isolate critical systems when you are not sure which systems are affected? Can you make containment decisions with incomplete threat intelligence?
- Real-time threat intelligence integrationLeverage automated threat feeds, OSINT collection and dark web monitoring to identify when your organization appears on leak sites or in threat actor communications, often before internal detection mechanisms are triggered.
- Patch management with risk prioritizationCVEs are not all the same. Develop frameworks that prioritize patches based on active exploitation, exploit availability, exposed attack surface and potential business impact, not just CVSS scores.
- Continuous tabletop exercisesRegularly simulate zero-day exploitation scenarios where detection occurs at the end of the kill chain. Test your team's ability to make critical decisions under uncertainty and time pressure.
Leveraging AI-driven analytics in incident response
Modern threat intelligence operations increasingly rely on machine learning models for rapid data analysis during active incidents. By analyzing the Harvard breach dataset, AI-powered tools enabled:
- Automated PII detection in unstructured data dumps using NLP models trained on regulatory definitions (GDPR, CCPA, HIPAA)
- Fingerprinting scheme to identify the specific ERP platform and version based on field naming conventions and data relationships
- Entity extraction to map organizational structure, supplier relationships and international operations from financial transaction records
- Temporal analysis to identify anomalous access patterns that suggest when initial compromise is likely to occur
These capabilities, accessible through mature CTI platforms with appropriate dark web access and data ingest pipelines, enable security teams to quickly assess the scope of the breach and prioritize response activities when every minute counts.
Final considerations
The Harvard-Cl0p incident is not about Harvard's security posture failing. It is about the asymmetric nature of modern cyber conflict. Attackers need to succeed once. Defenders need to succeed continuously. Zero days give adversaries windows of opportunity that no amount of investment in traditional controls can close.
The organizations that survive and recover from these incidents are not necessarily the ones with the largest security budgets. They are the ones that have mature incident response frameworks, crisis management protocols practiced y organizational resilience integrated into its culture.
When the next zero day falls, and it will, the question is not whether it will be compromised. It is whether it can detect, contain and recover while operating with partial information under extreme pressure.