Strategic guidance for information security managers
1. Factors with the greatest impact on cyber resilience.
A very interesting fact in determining the priority of initiatives in a cybersecurity program is to examine which factors contribute most to the cost of a cyber breach.
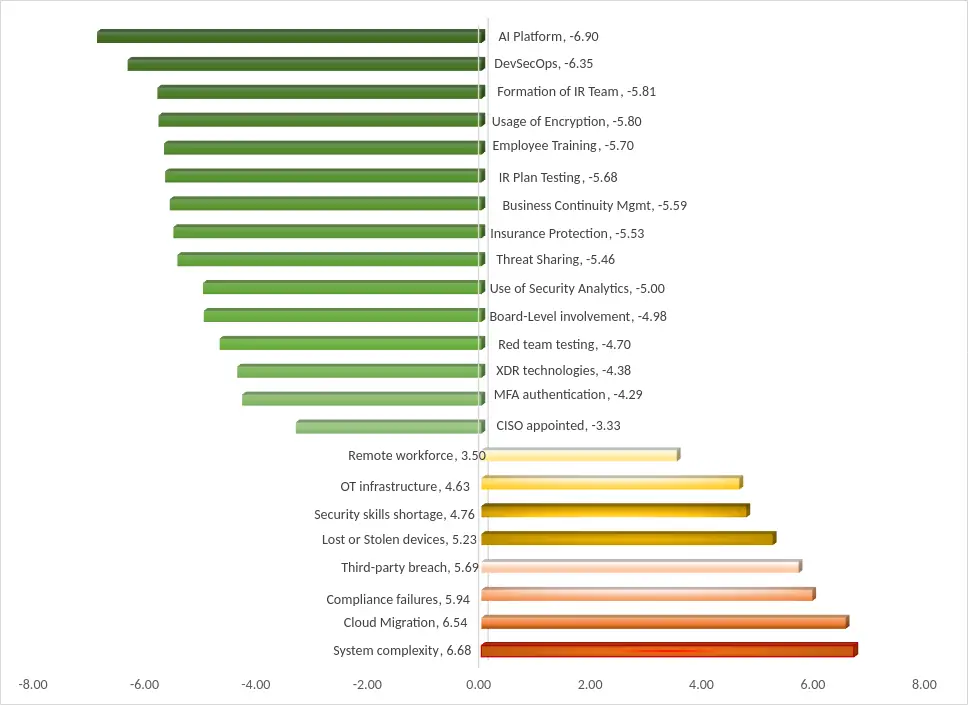
The main factors that can be taken into account are not only the maturity of an organization's practices, but also technologies and external factors. By comparing how the existence or absence of these factors is associated with below-average (cost-mitigating influence) or above-average (cost-amplifying influence) violation costs, we can get an idea of their importance.
Figure 5: Factors influencing the cost of a data breach. Source: IBM and Ponemon Institute, 2024. Figures represent the average percentage reduction or increase in the cost of a cyber data breach.
Since the data is shown in percentages, we can make some interesting deductions. For example, a healthcare organization with an average cost per cyber breach of $10.1 million can estimate a potential cost reduction of about $600,000 if it trains its employees in cybersecurity awareness.
While the consequences of data breaches are severe, there are concrete ways organizations can mitigate costs and improve their overall security posture. Key cost reduction factors identified in the research include:
- DevSecOps approach: the integration of safety in the life cycle of a product.
development reduces violation costs by approximately 20 %. - Incident response and testing team: organizations with a plan of
proven incident response record costs for security breaches
a 15 % minor. - AI and automation in security: the extensive use of AI and
automation in security correlates with a reduction of
costs higher than 20 %. - Employee training: regular training in awareness training
on safety reduces the costs of violations by approximately 5-6%.
%. - Cyber insurance: keeps the costs of violations stable and provides a stable
financial predictability.
When considering the first set of initiatives to be implemented in an organization beginning its cybersecurity journey, a CISO can start by first choosing a cyber insurance plan and incident response contract, progressively moving to the next steps on the ladder, following a risk mitigation language that the board can easily understand and support.
1. The FAIR methodology: a standard for quantitative analysis of cyber risk.
1.1 Introduction to FAIR
While the formulas and benchmarks presented in the previous sections provide CISOs with powerful tools for estimating cyber risk exposure, organizations seeking a more structured and internationally recognized approach to cyber risk quantification should consider implementing the Factor Analysis of Information Risk (FAIR) methodology. FAIR is the only international standard quantitative model for information security and operational risk. FAIR provides a model for understanding, analyzing and quantifying cyber and operational risk in financial terms. Unlike traditional risk assessment frameworks that rely on qualitative color charts or weighted numerical scales (high/medium/low), FAIR provides a methodology for breaking down risk into distinct measurable factors and for using statistics and probabilities to quantitatively estimate risk.
1.2 The architecture of the FAIR framework
The FAIR methodology has evolved beyond its original model to encompass a comprehensive framework for cyber risk management. Together with the original FAIR standard, FAIR-CAM and FAIR-MAM form the FAIR Framework for Cyber Risk Management.
The basic FAIR model
The FAIR methodology quantifies cybersecurity risk by breaking it down into individual factors through the use of statistical analysis and probabilities. It assesses risk through carefully defined scenarios, evaluating the likely frequency of loss events (loss event frequency) and the potential impact of those losses (loss magnitude). Balbix
The model decomposes risk into two main components:
Loss event frequency (LEF), which is determined by:
- Threat Event Frequency (TEF): the frequency with which a specific threat agent is likely to act against an asset.
- Vulnerability (Vuln): the probability that a threat event will result in a loss event, based on the capabilities of the threat vs. defenses of the asset.
Magnitude of loss (LM), which encompasses:
- Primary loss: direct costs resulting from lost productivity, response costs, replacement costs, fines and judgments, and loss of competitive advantage.
- Secondary loss: indirect costs arising from secondary stakeholder reactions, including reputational damage, legal fees and regulatory sanctions.
FAIR analysts always quantify risk not as a single value, but as a range of probable outcomes to account for the uncertainty of any business decision. This probabilistic approach, typically applied through Monte Carlo simulations, generates thousands of possible financial loss outcomes for a given risk scenario, along with the relative probability that each will occur.
FAIR-CAM: the control analysis model
FAIR-CAM takes the analysis of control systems to a granular level. It describes and quantifies the role of each control in reducing risk, documents the interdependence between controls and the effectiveness of a multiple control environment in general.
FAIR-CAM extends the FAIR model by classifying controls into three domains: loss event controls (reduce the frequency or magnitude of losses), variance management controls (ensure the reliability of controls) and decision support controls (align decisions with organizational objectives). This systemic perspective highlights the interdependencies between controls, which ensures a more reliable measurement of their effectiveness.
FAIR-MAM: The materiality assessment model
In addition, FAIR provides what they call the «Materiality Assessment Model (FAIR-MAM),» a mini-framework that provides a more detailed breakdown and description of the categories that contribute to the magnitude of losses, especially useful for determining when exposure to cyber losses becomes a material risk to an organization. This addresses the challenge of quantifying the financial impact of cyber incidents. By breaking down losses into different modules and categories, it allows analysts to provide more accurate and defensible estimates.
1.3 Implementation of FAIR in IT environments
In traditional IT environments, FAIR provides a structured methodology for assessing risks in enterprise applications, databases, networks and cloud infrastructure. The four-step implementation process follows a logical progression:
Stage 1: Identify and delimit risk scenarios This process begins by identifying assets that could be at risk, such as sensitive data, critical infrastructure or intellectual property. These assets are then linked to potential threats, referred to as «threat agents» or «threat communities.» Threat agents can range from cybercriminals and state actors to insider threats, such as disgruntled employees. Balbix
Stage 2: Evaluate the frequency of loss events Analysts estimate the frequency with which threat events could occur and the likelihood that these events will successfully circumvent defenses. This requires gathering threat intelligence data, historical incident information and vulnerability assessment results.
Stage 3: Assess the magnitude of losses Using FAIR- MAM's detailed taxonomy, analysts quantify potential losses in all categories, including impact on productivity, response costs, replacement costs, regulatory fines, legal fees and reputational damage.
Stage 4: Deriving and articulating risk Multiply the frequency of loss events by the magnitude of loss events to calculate the overall value of risk. TechTarget's Monte Carlo simulations generate probability distributions that communicate risk as ranges rather than single values, giving decision makers a realistic understanding of possible outcomes. FAIR supports smarter security decision making across a wide range of scenarios: budget justification (prioritize spending by impact, not guesswork), cloud transformation (assess risk in hybrid and multi-cloud environments), third-party/supplier risk (model potential losses from SaaS or IT service providers), board reporting (replace vague updates with quantified, reliable information), and compliance readiness (tie security controls to risk reduction, not just checkboxes). Principle
1.4 Application of FAIR in OT and ICS/SCADA environments
The convergence of information technology (IT) and operational technology (OT) has created new challenges for risk quantification. Industrial control systems (ICS) and supervisory control and data acquisition (SCADA) systems present unique risk characteristics that FAIR is well equipped to address.
Understanding OT risk factors
OT environments differ fundamentally from traditional IT in several ways that affect risk assessment:
Historically, ICS environments operated in isolated networks with limited external connectivity, reducing the perceived need for robust security measures. These systems relied heavily on vendor-specific hardware, software and communication technologies, making them less adaptable to modern security practices. As a result, many legacy ICS devices continue to use outdated operating systems, as well as legacy protocols that lack encryption or authentication mechanisms.
Application of FAIR to TO risk scenarios
- Because of all these factors, when quantifying cyber risk in OT environments, loss magnitude calculations must go beyond traditional financial metrics and include:
- Safety impact: potential for physical harm to personnel or surrounding communities.
- Environmental consequences: risks of chemical emissions, pollution or ecological damage. Production interruption: loss of revenue due to operational downtime in manufacturing or critical infrastructure.
- Chain effects: secondary failures that can propagate through interconnected systems.
For example, a FAIR analysis of a ransomware scenario targeting the HMI (human-machine interface) systems of a manufacturing plant would take into account:
- Frequency of threat events: likelihood of ransomware operators attacking industrial systems (based on threat intelligence from groups such as ALPHV or LockBit).
- Vulnerability: effectiveness of network segmentation between IT and TO zones, patch status of HMI software and effectiveness of backup systems.
- Magnitude of the loss: costs per hour of production downtime, potential for safety incidents, regulatory penalties under industry-specific requirements, and recovery costs for potentially isolated restoration
1.5 From qualitative to quantitative: the business case
The transition from qualitative to quantitative risk assessment represents more than a methodological change, as it fundamentally transforms the way cybersecurity is perceived and prioritized at the executive level.
The board is not driven by fear (unless you were hired as CISO right after an incident...), but it is driven by financial impact and ROI. FAIR allows security teams to speak your language. Instead of saying, «We need MFA because it's critical,» you say, «We have a $2.4 million exposure from credential-based attacks, we need a tool like Adiscovery that counters that exposure at a cost of less than $100,000.».
For CISOs presenting to boards of directors, FAIR provides a defensible, financially based analysis that transforms cybersecurity from a technical cost center to a strategic business function. When combined with the breach cost data and impact formulas presented earlier in this guide, FAIR completes the picture by providing a standardized, repeatable methodology for ongoing quantification of risk that evolves with the threat landscape and organizational changes.
2. Quantifying cyber risk: putting it all together.
Throughout this guide, we have built a comprehensive, data-driven foundation for CISOs to address their boards with confidence and credibility. Let's summarize the key ideas:
1. Cyber risk is the fastest growing business concern globally. From being a minor consideration in 2014 (ranked 15th), cybersecurity has risen to become the number one risk facing organizations around the world, surpassing even pandemic and geopolitical concerns. This trajectory shows no signs of reversing.
2. The financial impact continues to increase. The average cost of data breaches has steadily increased, reaching $4.35 million globally by 2022, with U.S. organizations facing costs more than double this average. Healthcare, financial services and technology sectors bear the highest costs.
3. Quantification enables strategic conversations. Using the formulas provided (cost of downtime, cost of productivity and lost revenue), CISOs can translate abstract cyber risk into concrete financial terms that resonate with board members and executives.
4. Insurance and IR retention contracts provide immediate risk reduction. While not miracle solutions, these investments offer financial protection and rapid response capabilities that can dramatically reduce the total cost of incidents. The return on investment is compelling: typical investments represent between 2 % and 3 % of potential exposure to a single incident.
5. Data-driven prioritization guides program development. Research on cost drivers provides a roadmap for security investments, helping CISOs prioritize initiatives such as DevSecOps, IR planning, security automation and employee training based on demonstrated impact.
Once an organization has a clear understanding of its vulnerabilities and potential risks, it can begin to more accurately quantify the cyber risk it faces. This involves assessing the likelihood of various threats, such as malware infections, phishing attacks, insider threats or advanced persistent threats (APTs), and estimating their potential impact, including financial losses, data breaches, operational disruptions and reputational damage.
To effectively quantify cyber risk, organizations often employ methodologies and frameworks such as risk assessment models, threat intelligence analysis, vulnerability analysis and penetration testing. These methods help identify and prioritize the most significant risks and guide the development of a sound cyber defense strategy.
By quantifying cyber risk, organizations can better understand the potential consequences of cyber threats and make informed decisions about resource allocation. This understanding enables them to prioritize investments in cybersecurity measures and establish a well-defined budget for their strategic cyber program. In addition, quantifying cyber risk helps organizations demonstrate the value of their cybersecurity initiatives to stakeholders, justify funding requests, and align security efforts with business objectives.
The path forward for every CISO starts with data. With the frameworks, formulas and benchmarks presented in this guide, you will be prepared to transform cybersecurity from a cost center into a strategic enabler, protecting the organization while demonstrating clear business value to your board and stakeholders.
References
- Allianz Risk Barometer (2012-2024). Annual global corporate risk survey. Allianz Global Corporate & Specialty.
- IBM Security and Ponemon Institute. Cost of Data Breaches Report (2013-2024).
- Cybereason (2022). «Ransomware: the true cost to businesses.» https://www.cybereason.com/ransomware-the-true-cost-to-business-2022
- Allianz Global Corporate & Specialty (2015). «Cyber risk guidance: managing the impact of increasing interconnectivity.».
- Financial Times. «Risk managers warn that cyber insurance could become an unviable product.».
- Gartner (2014). «The cost of downtime.».
- Ponemos Institute (2016). «Cost of service interruptions in data centers».