Strategic guidance for information security managers
Introduction
In today's increasingly interconnected and digitized world, organizations face a growing threat of cyber-attacks. These attacks can lead to significant financial losses, reputational damage and even the disruption of critical business operations. To mitigate these risks, it is critical that organizations quantify the cyber risks to which they are exposed and develop a comprehensive strategic cyber program.
Quantifying cyber risk involves assessing the likelihood and potential impact of various cyber threats and vulnerabilities specific to an organization. By understanding the potential risks, organizations can make informed decisions about resource allocation and budgeting for their cyber defense initiatives.
For a newly embedded CISO, this can sometimes pose a «chicken or the egg» problem. If they follow the mature, methodological approach to cyber risk management and quantification, before establishing the initial steps to budget for a strategic cyber program, they must first assess their organization's existing security posture and identify potential vulnerabilities. This assessment should include evaluation of the organization's network infrastructure, data protection mechanisms, employee awareness and training, incident response capabilities, and compliance with relevant regulations.
Now, let's forget for a moment an ideal situation: the CISO needs support (money, resources and time) before he can even begin to do any of these things. How can he get the backing of the board of directors?
One way to achieve this (never better said) is to show them the current risk levels of similar organizations, either by market sector or by geographic area.
With this in mind, we have created this guide for those CISOs who wish to: first, budget the necessary spend on a strategic cybersecurity program; second, gather data from other similar organizations to compare the organization's cybersecurity requirements; and finally, take the first steps to address the key risks facing the organization while the program is not yet in place.
1. The strategic importance of cyber risk
Over the past 25 years, the world has witnessed a remarkable transformation driven by technological advances, communication technologies and the global reach of information. Unfortunately, the advent of a globally interconnected world brought with it a whole new set of risks that organizations must contend with: cyber risks. With each new technological advancement, the cybersecurity landscape continues to change, and attackers are constantly finding new ways to circumvent organizations' security controls and steal valuable data. Companies must prioritize how to defend themselves.
But to what extent should they? For most of us, even the term «cyber» meant nothing in 2000, and evoked only vague references to the movie «Hackers,» starring Angelina Jolie in the late 1990s. By the 2000s, the Internet was becoming a ubiquitous force in our lives, but the potential risks and vulnerabilities were not fully understood. Cybercriminals began to exploit these weaknesses, launching attacks that stole information from organizations, disrupted critical infrastructure and undermined trust in digital systems. Viruses, worms and malware proliferated, wreaking havoc on individuals and organizations alike.
Progressively, as the frequency and severity of cyberattacks increased, so did the response. Governments, businesses and individuals recognized the need to strengthen their defenses. Over the years, we have witnessed advances in cybersecurity practices and technologies. Governments created dedicated cybersecurity agencies and developed comprehensive strategies to protect their countries' critical infrastructures. International collaborations emerged to share threat intelligence and foster cooperation against cybercrime.
In parallel, the private sector invested heavily in research and development, resulting in innovative cybersecurity solutions. Machine learning and artificial intelligence were leveraged to detect and respond to threats in real time. Encryption technologies became more robust, protecting data from unauthorized access. Companies implemented strict security protocols and employee awareness programs, recognizing that human error can be a significant vulnerability.
In addition, the evolving threat landscape demanded a more proactive approach. Instead of relying solely on reactive measures, organizations began to adopt proactive strategies such as threat hunting and penetration testing. The concept of «defense in depth» took hold, emphasizing multiple layers of protection to mitigate risks holistically. Incident response and recovery plans were developed to minimize the impact of attacks and enable rapid recovery.
1.1 Cyberspace as a source of business risk
The Allianz Risk Barometer is an annual report published by Allianz, the insurance and asset management company. It provides information on the main risks and concerns facing companies around the world, based on a survey of risk experts, including risk managers, underwriters, brokers and insurance professionals, from various industries and regions. The survey aims to identify and rank the most important risks that companies expect to face in the coming year. It has been published for more than 12 years, with the first version published in 2012.
Collecting and analyzing these global statistics over the last decade allows us to track how cyberspace has become the biggest source of risk for organizations around the world. In addition, as we will see, it can also relate to trends in Internet usage, mobile device penetration, research and development spending, disease prevalence, literacy rates and access to education. These statistics can be the first step in our journey as CISOs: making evidence-based decisions and identifying areas where specific interventions can drive positive change.
Now, let's examine the data: until 2014, cybersecurity as a source of risk was considered a minor concern. In fact, it suddenly appeared in the rankings by being named an «emerging hidden risk» in the Allianz report, moving from 15th to 8th place.
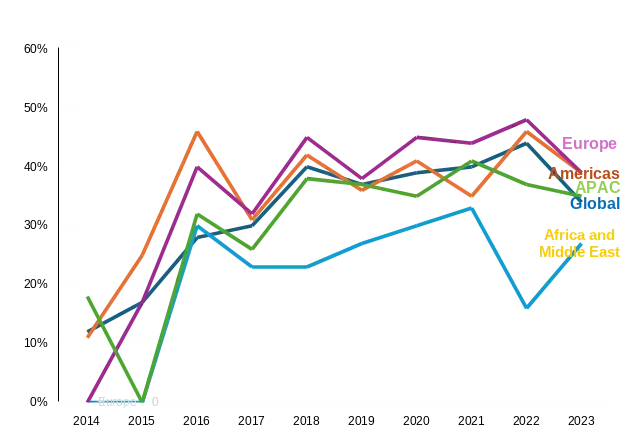
Source: Allianz Risk Barometer, A&M analysis Figures represent the ranking of cyber risks as a source of selected risks as a percentage of annual respondents.
Figure 1: Evolution of the classification of cyber risks (2012-2023). Source: Allianz Risk Barometer. Figures represent the ranking of cyber risks as a selected source of risk as a percentage of annual respondents.
Since then, cyber incidents have steadily increased each year, eventually becoming the leading cause of risk globally. Not only that, by comparison, not even COVID-19 at the peak of the pandemic, nor the energy crisis stemming from the Ukraine-Russia war have garnered as much attention as a source of potential disruption to operations.
Source: Allianz Risk Barometer, A&M analysis Figures represent the ranking of cyber risks as a source of selected risks as a percentage of annual respondents.
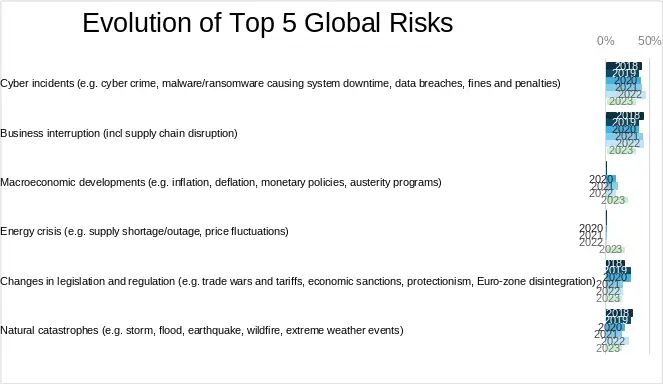
It is also worth noting that cyberattacks share the global top spot in these statistics with business interruption, which is not mutually exclusive: a cyberattack, such as a denial-of-service attack, ransomware encryption or other types of cyber extortion, can cause a company to cease operations.
Cyber incidents topped the risk barometer survey for the first time in 2020, and again in 2022 and 2023. The main factor has been the rise of larger and more sophisticated ransomware attacks. These include worrying trends such as «double extortion» tactics, which combine system encryption with data breaches, as well as several cases of massive global-scale exploitation of third-party software vulnerabilities that could affect thousands of companies (e.g., Log4J, Kaseya) or target critical physical infrastructure (the Colonial Pipeline in the United States).
What is the main conclusion that should guide our initial conversation about managing these risks? First: cybersecurity is the fastest growing concern for all companies globally: it is here to stay and will continue to be a major issue for the foreseeable future.
1.2 Cyber risk finance
We now have a strategic driver, which is likely to attract the attention of the board of directors. It's time for the CISO to put some numbers on the table: from a purely financial point of view, how much can the materialization of a cyber risk affect our organization?
We will try to answer this question in more detail later, but for the sake of simplicity, let's start with an initial estimate: how much would a single cyber incident or breach cost? And, again, let's use collected and published data to provide an answer. For the past decade, IBM and the Ponemon Institute have collaborated to publish an annual report on cybersecurity incidents called the Cost of Data Breach Report. This report analyzes actual data breaches suffered by organizations in a variety of industries, examining the causes, costs and consequences of data breaches, with the goal of providing organizations with a comprehensive understanding of the potential risks and financial implications they may face in the event of a breach.
One of the highlights of the report is the calculation of the average cost of a data breach. This includes direct costs, such as incident response, notification and legal fees, as well as indirect costs related to reputational damage, lost customers and lost business opportunities. The report also breaks down these costs by region, industry and size of the affected organization.
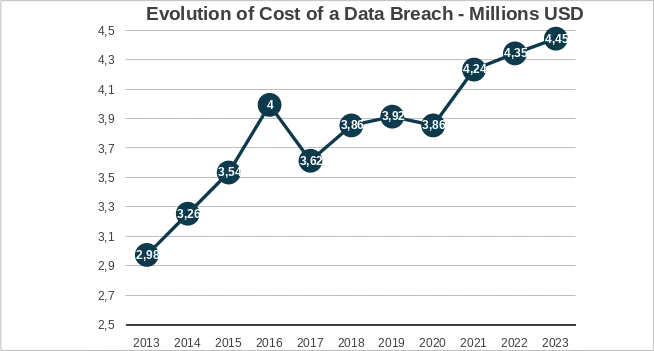
Figure 3. Evolution of the cost of a data breach - Millions of US dollars. Source: IBM and Ponemon Institute, Apeiroo analysis The figures represent the cost in millions of US dollars of a cyber data breach.
We can draw a parallel with the above statistics: as the financial impact of cyber risks increases, so does the perception and concern of organizations to address them.
This, in the hands of a CISO, gives us a simple but compelling argument: who wouldn't want to avoid a $4 million cost to their organization?
Data-driven cyber risk quantification for CISOs Page6 of 2 We can also further analyze the data by geography: as expected, U.S. organizations face the highest costs when they suffer cyber breaches, more than double the global average of $4.35 million in 2022.
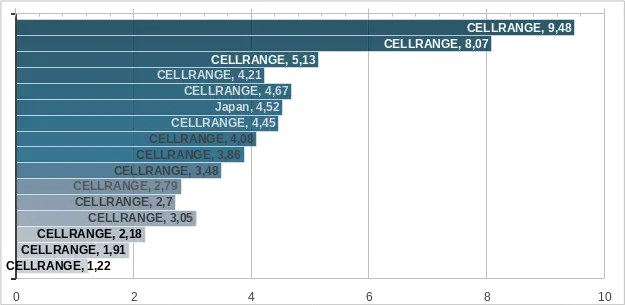
Source: IBM and Ponemon Institute, Apeiroo analysis, 2025 data Figures represent the cost in millions of US dollars of a cyber data breach.
At first glance, it is clear that the costs are steadily increasing. A small organization may not be able to survive the costs associated with a cybersecurity breach and, in fact, some studies clearly reflect this. For example, a study by Cybereason revealed that, in 2022, a staggering 33 % of companies affected by cyber ransomware were forced to temporarily suspend business while under attack.
Cyber Insurance and Incident Response Preparedness
2.1 The evolution of cyber insurance
Cyber liability insurance, also known as cyber insurance, is a type of insurance that provides coverage for losses and damages resulting from cyber attacks, data breaches and other types of cyber incidents.
In 2015, Allianz published the first global report on cyber insurance, which stated, «The cyber insurance market is currently estimated to be worth approximately $2 billion in premiums worldwide, with U.S. companies accounting for approximately 90 %.» It is believed that less than 10 % of businesses currently take out cyber insurance. However, the cyber insurance market is expected to grow at a double-digit rate year-over-year and could reach $20 billion or more in the next 10 years.».
That prediction has proven to be very accurate. The global cyber insurance market has experienced exponential growth, driven by the increasing frequency and sophistication of cyber attacks, tightening regulatory requirements for data protection, and growing board and executive awareness of cyber risk as a major threat to businesses. By 2023, the market had effectively passed the $20 billion mark, with forecasts suggesting it could reach $40-50 billion by 2030.
This growth reflects a fundamental shift in the way organizations perceive cyber risk from an IT problem to a strategic business risk requiring financial hedging. The COVID-19 pandemic accelerated this trend, as rapid digital transformation exposed new vulnerabilities and telecommuting dramatically expanded the attack surface.
2.2 What cyber insurance covers
Cyber liability insurance typically covers the following:
- Data breaches: coverage of the costs of responding to and managing a data breach, including notification costs, credit monitoring services, public relations and legal fees.
- Business interruption: coverage for losses resulting from downtime caused by a cyber incident, including lost income and additional expenses.
- Ransomware attacks: coverage for the costs of responding to a ransomware attack, including payment of ransom demands (where legal), data recovery and business interruption losses. - Cyber extortion: coverage for costs incurred in response to cyber extortion threats, such as ransom demands or threats of website attacks.
- Liability: coverage for third-party claims arising from a cyber incident, such as customer lawsuits or regulatory sanctions.
- Cybercrime: coverage for losses resulting from cybercrime, such as online fraud or theft of electronic funds.
2.3 The changing landscape: insurance is not a panacea
While cyber insurance is a critical element in ensuring that your business can recover from a cyberattack, organizations are facing a completely different landscape today. As highlighted in a Financial Times article titled «Risk managers warn that cyber insurance could become an »unviable product,'" the industry is facing unprecedented challenges.
Insurance companies have significantly tightened their underwriting requirements. Organizations are now required to demonstrate their ability to defend against ransomware attacks through a wide range of security controls. For example, insurers now require specific security measures to be implemented e , including multi-factor authentication (MFA) to prevent the spread of ransomware incidents. Other common prerequisites include endpoint detection and response (EDR) solutions, regular patching, privileged access management and proven incident response plans.
The key takeaway for CISOs: cyber insurance should not be sold to the board as a «silver bullet» solution to address cyber risk. Instead, they should be positioned as a component of a comprehensive risk management strategy, an initial step along the way that provides financial protection while the organization develops its security maturity. The insurance application process itself can serve as a valuable exercise, as it forces organizations to evaluate their security posture against industry standard controls.
Incident response contracts: an essential investment:
- An incident response contract provides organizations with a structured form of expertise and support through a security partner, enabling them to respond quickly and effectively in the event of a cyber incident. Having an incident response contract in place allows you to benefit from proactive support to protect your operations, your reputation and your bottom line.
- Many privacy and consumer protection laws, such as GDPR (72-hour notification requirement) and several U.S. state breach notification laws, require timely response and notification of cyber incidents. Having a contract in place reduces the difficulty of finding specialized support in the event of a major incident affecting many organizations simultaneously, when demand for incident response services peaks and availability is low.
- Key benefits include: guaranteed response times (typically 2-4 hours), pre-negotiated rates, established communication protocols, familiarity with your environment (through regular assessments) and access to expertise such as forensic analysis, legal advice and crisis communications.
To effectively quantify cyber risk, organizations often employ methodologies and frameworks such as risk assessment models, threat intelligence analysis, vulnerability analysis and penetration testing. These methods help identify and prioritize the most significant risks and guide the development of a robust cyber defense strategy.
By quantifying cyber risk, organizations can better understand the potential consequences of cyber threats and make informed decisions about resource allocation. This understanding enables them to prioritize investments in cybersecurity measures and establish a well-defined budget for their strategic cyber program. In addition, quantifying cyber risk helps organizations demonstrate the value of their cybersecurity initiatives to stakeholders, justify funding requests, and align security efforts with business objectives.
The path forward for every CISO starts with data. With the frameworks, formulas and benchmarks presented in this guide, you will be prepared to transform cybersecurity from a cost center into a strategic enabler, protecting the organization while demonstrating clear business value to your board and stakeholders.
References
- Allianz Risk Barometer (2012-2024). Annual global corporate risk survey. Allianz Global Corporate & Specialty.
- IBM Security and Ponemon Institute. Cost of Data Breaches Report (2013-2024).
- Cybereason (2022). «Ransomware: the true cost to businesses». https://www.cybereason.com/ransomware-the-true-cost-to-business-2022
- Allianz Global Corporate & Specialty (2015). «Cyber risk guidance: managing the impact of increasing interconnectivity.».
- Financial Times. «Risk managers warn that cyber insurance could become an unviable product.».
- Gartner (2014). «The cost of downtime». 7. Ponemon Institute (2016). «Cost of service disruptions in data centers».