Strategic guidance for information security managers
1. Calculating the impact of cyber incidents.
Let's continue our journey to understand how to use data to drive our strategic decisions on developing and budgeting our cyber strategy.
Several attempts have been made to calculate the hourly cost of downtime for an organization facing a cyber incident (regardless of type).
In 2014, a Gartner study on the cost of downtime yielded an estimate of $5600 per minute. Later, in 2016, the Ponemon Institute estimated the figure at $9000 per minute.
Regardless of the business, and although it varies by company, a cyber incident is always costly. However, using an average derived from data from leading companies may not adequately help a CISO convince the board of directors of the need to invest in cyber strategy. Therefore, to provide something meaningful to your organization, we must use a calculator and your own company's data.
Although neither the Ponemon Institute nor Gartner disclose the formulas they use to quantify the economic amounts derived from data breaches, they clearly state that they have taken into account legal, regulatory and technical activities, as well as estimating the loss of brand value, customer churn and decreased employee productivity.
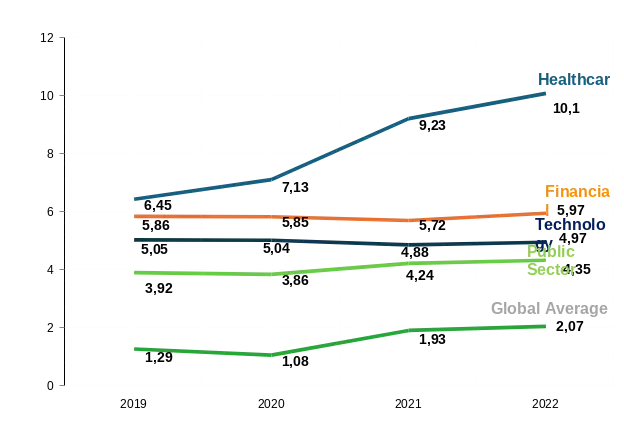
SourceIBM and Ponemon Institute, analysis by Apeiroo
The figures represent the cost in millions of US dollars of a cyber data breach.
All of these elements give us clues on how to make our own calculations about cyberincident finances. In the interest of transparency, we have decided to shed some light on these components. We find it very unfortunate that no previous study has published a clear methodology for CISOs to calculate for themselves the costs of a cyber incident. This is our attempt to calculate the approximate cost of cyber incidents, taking into account direct, indirect and opportunity costs:
- Direct costs: The direct cost of carrying out a given activity (e.g., hiring external incident response consultants, outsourcing the telephone help desk).
- Indirect costs: The amount of time, effort and other organizational resources expended, but not as a direct cash outlay (e.g., internal investigations, internal communications).
- Opportunity costs: Costs arising from lost business opportunities as a result of negative reputational effects after the breach has been communicated to victims and publicly disclosed to the media.
1.1 Calculation of salary cost for downtime
Calculating the financial impact on productivity is a simple process:
Step 1: Determine the average hourly wage of the affected employees. This can be easily obtained through the human resources department. An average estimate that is not too far from the fully validated figure is acceptable.
Step 2: Decide the productivity impact factor of the downtime event. (For example, if your primary Internet connection is lost due to a denial-of-service (DDoS) attack and you have no backup, what would that mean for all of your departments?) This could be as low as 10 % or as high as 100 %, depending on what the disruption is and the nature of the work of the affected employees.
Cost of downtime = E × I% × S
Where:
- E = Number of employees affected
- I% = Productivity factor (percentage affected by the incident)
- S = Average hourly wage
Example: in a team with 500 professional employees operating in a fully cloud-based model, the calculation would be as follows: 87.97 $ (average hourly wage) × 90 % (estimated level of impact on productivity) × 500 (number of employees concerned) = 39 586.50 $ per hour.
This is the direct internal cost to the company, in wages alone. But what about compliance and opportunity costs?
1.2 The total cost method
If we want more detail to describe the magnitude of the problem to the organization's decision makers, we need to take a few more steps. One comprehensive method is to add the direct internal costs (the money the organization will actually lose) to the revenue costs (the lost revenue that cannot be collected from customers during the downtime).
Productivity cost formula
Productivity cost = E × I% × C × H
Where:
- E = Number of employees affected
- I% = Percentage by which they are affected (e.g., can they continue to perform the
50 % of your work even after access to the application is interrupted?
- C = Average hourly cost of an employee for the company (including 30 % of
overhead costs for training, electricity, rent, etc.)
- H = Number of hours of inactivity
Loss of income formula
Loss of income = (GR / AH) × I% × H
Where:
- GR = Gross income (annual)
- AH = Total number of working hours (annual). A valid estimate: 220 days
× 8 hours = 1760 hours per employee
- I% = Percentage of impact on earning capacity
- H = Number of hours of inactivity
1.3 Recovery and compliance costs
The calculation of recovery and compliance costs has no objective formula, so here we must use discretionary estimates based on your organization's specific circumstances. In developing your estimate, you should consider the following activities:
- Incident investigation: internal IT and security team hours, plus external forensic investigators if required. Typical forensic investigation jobs range from $25,000 to over $250,000, depending on complexity.
- Determining the scope of the data breach: Identification of affected data subjects for potential regulatory disclosure and notification to customers. This usually requires specialized data mining and analysis tools.
- Preparation of notification documents and required disclosures: legal counsel fees, regulatory filings and customer notification costs. Notice costs per filing typically range from $1 to $5 per affected person, plus legal fees of $200 to $500 per hour.
- Credit monitoring and identity protection services: often necessary or expected in case of breaches involving personal data.
Typical costs: $10 to $30 per year per affected person.
- System remediation and hardening: costs to fix vulnerabilities, rebuild compromised systems and implement additional security controls to prevent reoccurrence.
- Post-incident training: refresher safety training and specific training on lessons learned from the incident.
1.4 Cost-benefit analysis: insurance and returns
The following examples demonstrate how investing in cyber insurance and an incident response retainer can far outweigh the potential costs of cyber risk materializing in business downtime.
Example 1: Medium-sized financial services company
Organization profile: 500 employees, $150 million in annual revenues, average salary of $95,000 per year ($45.67 per hour).
| Investment | Annual cost |
| Secure cyber ($5 million coverage) | 75,000$ |
| Investor Relations Retentions (100 hours per year) | 35,000$ |
| Total annual investment | 110,000$ |
Potential costs of a 48-hour ransomware incident (without insurance):
- Productivity loss: 500 × 80 % × 45.67 $ × 48 = 877 000
- Loss of income: ($150 million / 1760) × 75 % × 48 = 3 068 000
- Emergency Incident Response Services (no retainer fee): 150 000
- Recovery and repair: 500 000 $
• Total potential exposure: 4 595 000 $
Return on investment: The annual investment of 110,000 $ represents only 2.4 % of the potential exposure from a single incident. Even if the organization suffers only one significant incident every 5 years, the investment generates a return of 7.4:1.
Example 2: Healthcare organization
Organization profile: 2000 employees, annual revenues of $400 million, average cost of breaches in healthcare: $10.1 million (according to IBM/Ponemon)
Recommended investment:
- Cyber insurance (US$10 million coverage): US$200,000/year
- Public relations retentions (200 hours per year): US$65,000 per year
- Total: US$ 265,000 per year (2.6 % of the average cost of an infraction)
Given the high costs of breaches in the healthcare industry and the regulatory exposure under HIPAA, this investment provides critical financial protection while the organization develops the maturity of its security program.
References
- Allianz Risk Barometer (2012-2024). Annual risk survey
Global Corporate & Specialty. Allianz Global Corporate & Specialty.
IBM Security and Ponemon Institute. Report on the cost of data breaches
(2013-2024).
3. Cybereason (2022). «Ransomware: the true cost to businesses».
https://www.cybereason.com/ransomware-the-true-cost-to-business-2022
4. Allianz Global Corporate & Specialty (2015). «Cyber Risk Guidance:
managing the impact of increasing interconnectivity».
5. Financial Times. «Risk managers warn that cyber insurance.
could become an unviable product.
6. Gartner (2014). «The cost of downtime.».
7. Ponemon Institute (2016). «Cost of outages in data centers".
data».